Talks
What’s unique about our event is the trainings + talks format. Our two- and four-day hardware security trainings are supplemented with technical talks by selected speakers. One talk will be given during the lunch break on each training day. Only students registered for our training classes will have the opportunity to see these talks, so sign up now! Every speaker at our conference is also a student at our trainings.
Upcoming Talks
Common Embedded Device Vulnerabilities
Speaker: Rob Wood
Fault injection attacks, side-channel attacks, cryptographic attacks, and invasive silicon attacks are all well and good, but what about the security basics? You need to crawl before you can walk.
Read More…
Bluetooth Reverse Engineering Techniques and Tools
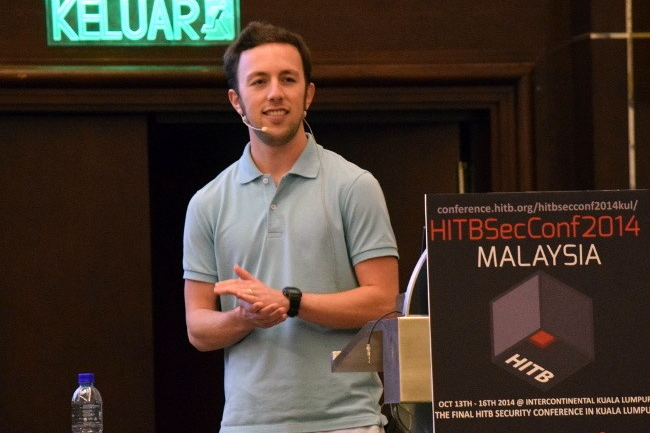
Speaker: Mike Ryan
With the continuing growth of IoT, more and more devices are entering the market with Bluetooth. Maybe you're developing one of your own. This talk aims to shed some light on how these devices use Bluetooth and will cover reverse engineering techniques that in many cases can be accomplished with hardware you already have!
Read More…
TPM Genie: Undermining the Hardware Root of Trust via Serial Bus Attacks
Speaker: Jeremy Boone
TPM Genie is a serial bus interposer that is designed to assist vulnerability research on Trusted Platform Modules. Levering TPM Genie, I demonstrate how to undermine most of the stated purposes of the Trusted Platform Module - measured boot, remote attestation, sealed storage, and the hardware RNG.
Read More…
RF Attacks in the Analog Domain
Speaker: Samy Kamkar
The invisible world of RF and EM is extremely exciting, especially as new protocols, safeguards, and attacks are revealed. Often researchers and attackers will employ complicated devices, circuits, or expensive equipment to pull off attacks. We'll show that with just a handful of discrete components and common microcontrollers, you can build attacks tools very easily, for example against point of sale systems, vehicles, hotels, and more.
Read More…
Event Details and Registration
For dates, the venue location and discounted hotel rates, please visit our venue page. To see our talks and attend our event, simply register for our upcoming trainings.